malware attack vectors
Ransomware Malware Vector Hacker Attack Infographic Illustration. 8 Pics about Ransomware Malware Vector Hacker Attack Infographic Illustration : Computer Malware Attack Stock Photo - Download Image Now - iStock, Ransomware Malware Vector Hacker Attack Infographic Illustration and also Malware Payloads Hide in Images: Steganography Gets a Reboot | Threatpost.
Ransomware Malware Vector Hacker Attack Infographic Illustration
 depositphotos.com
depositphotos.com
malware ransomware
Computer Malware Attack Stock Photo - Download Image Now - IStock
 www.istockphoto.com
www.istockphoto.com
malware attack computer virus antivirus representing skull software code screen
Observations Of ITG07 Cyber Operations - Malware News - Malware
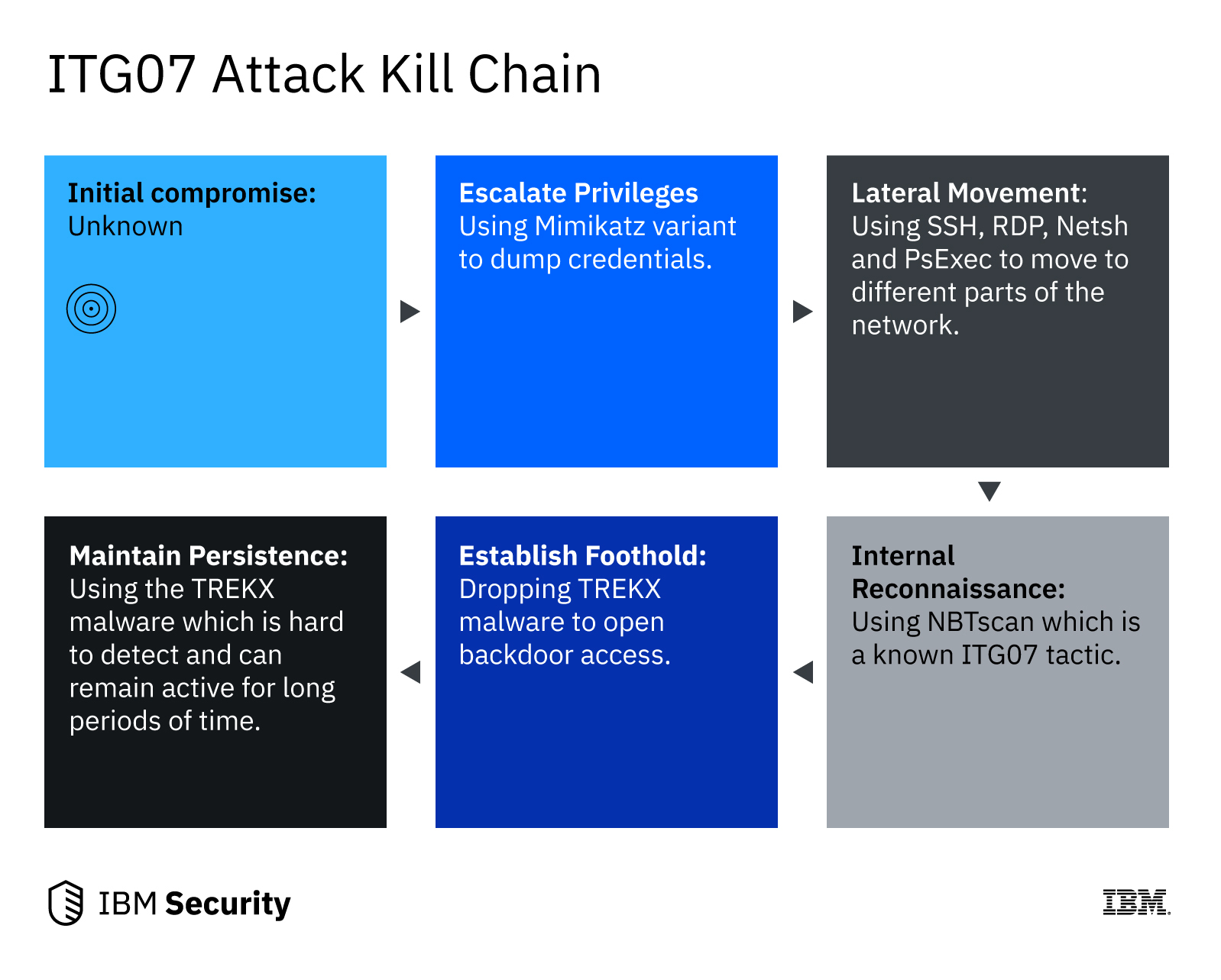 malware.news
malware.news
malware
Banks And Merchants Are Struggling To Keep Pace With Cyber Threats
 www.paymentscardsandmobile.com
www.paymentscardsandmobile.com
cyber cyberattack industries threats banks under chart pie merchants struggling pace keep showing
5 Cyber Attack Developments Worth Your Attention | Radware Blog
 blog.radware.com
blog.radware.com
mosys developments radware turbulent
The 10 Most Common Application Attacks In Action
 securityintelligence.com
securityintelligence.com
application network security attacks types threats common web diagram most prevention intrusion different firewalls attack systems port type action defenses
Malware Payloads Hide In Images: Steganography Gets A Reboot | Threatpost
 threatpost.com
threatpost.com
steganography payloads reboot malware hide gets threatpost
Malware And Botnet Attack Services Found On The Darknet | Radware Blog
 blog.radware.com
blog.radware.com
security malware iot botnet cyber idg connect service nightmare attacks defending denial against scherlund define policy threats destruction cybersecurity risk
Steganography payloads reboot malware hide gets threatpost. Application network security attacks types threats common web diagram most prevention intrusion different firewalls attack systems port type action defenses. Banks and merchants are struggling to keep pace with cyber threats